Security
The information below discusses the policies and procedures Customer.io has in place when dealing with Customer data.
See our full security policy
You can read more about our security practices on our website and download our compliance documents.
We use Bank-grade encryption
Customer.io uses 128-bit SSL encryption for all authenticated sessions. We support TLS version 1.2 and above. This means that data sent to the Customer.io API as well as data retrieved through the Customer.io management interface is protected.
You are limited to retrieving only your data
Data stored in your Customer.io account is only available to you. Each request to retrieve data from Customer.io must be authenticated. Furthermore, requests are restricted to the currently logged-in account. Requests made to the Customer.io internal API require a logged in account and will not return successfully otherwise.
We never store your credit card info
When you purchase a paid Customer.io subscription, your credit card data is not transmitted through nor stored on our systems. Instead, we depend on Stripe, a company dedicated to this task. Stripe is certified to PCI Service Provider Level 1, the most stringent level of certification available. Stripe’s security information is available online.
We require 2FA on all non-SSO accounts
If you use Customer.io as your identity provider (IDP), we require two-factor authentication (2FA) for you to finish signing in. By default, we email you a magic link after you submit your username and password. You can also use an authenticator app such as 1Password or Google Authenticator.
If you use Single Sign-on (SSO), we do not require 2FA. In this case, authentication is managed by your SSO provider.
We log you out after 14 days
If you use Customer.io as your identity provider, that is, you sign in using an email and password, your session will expire after 14 days. This includes accounts with two-factor authentication. This reduces the risk of hackers taking advantage of your account in a shared computing setting. The session will expire regardless of whether you’re active or not within the platform.
Your session will not expire if you use SSO.
Re-authenticate before your session expires
If you are logged into the platform, you’ll see a modal window two hours ahead of session expiration prompting you to re-authenticate and renew your session for another 14 days. If you don’t re-authenticate after two hours, you’ll be automatically logged out and lose all unsaved changes.
Similarly, if you need to reset your password, you will have to follow the “Forgot password?” flow which includes logging out and so, losing unsaved changes. We recommend using a password vault to avoid this situation.
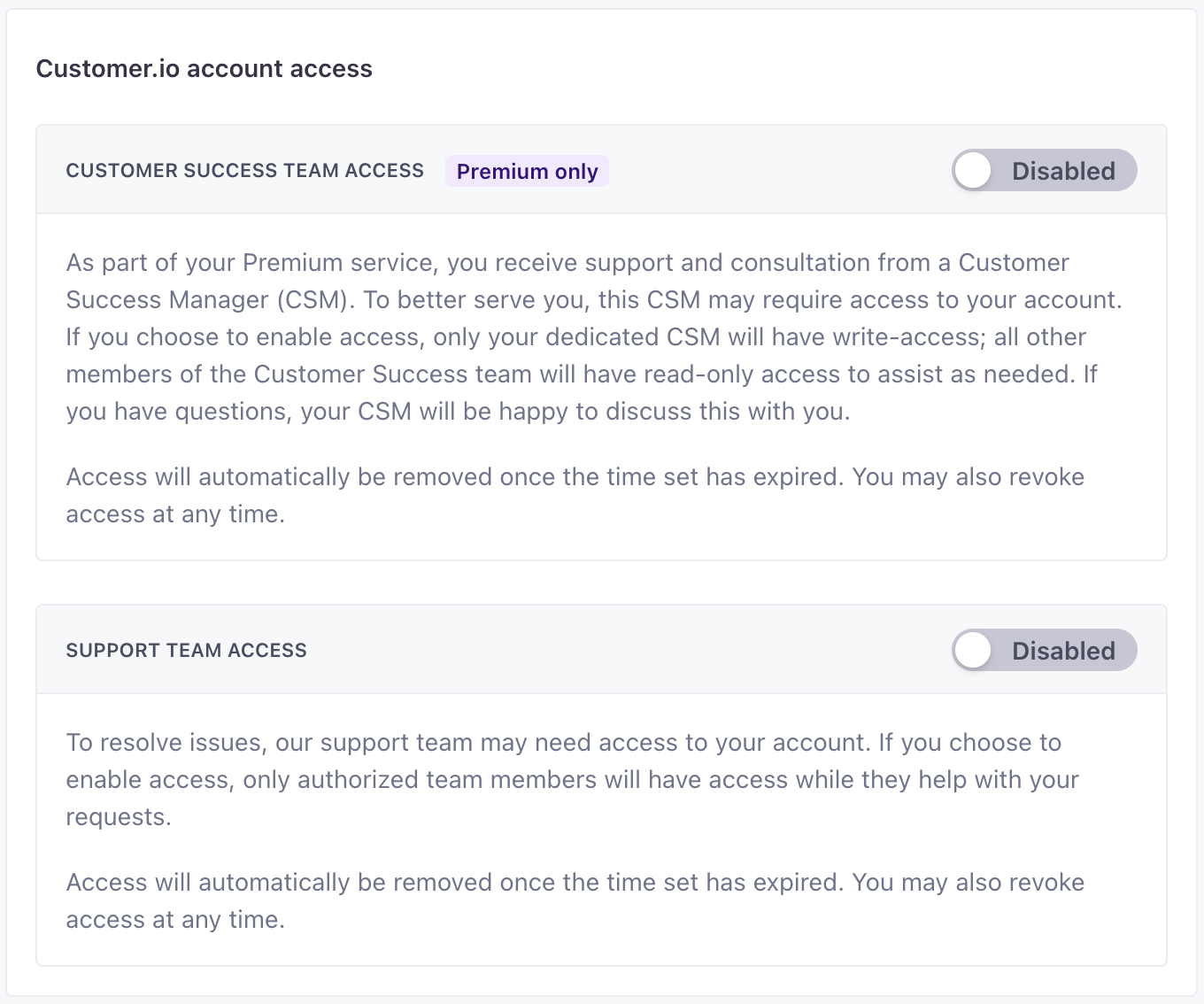
Customer.io employees have restricted access
Access to our servers is restricted to infrastructure engineers and maintenance staff. This access is granted through a unique key that can be revoked if necessary.
Customer.io employees cannot access your account, workspaces, or the data you store in Customer.io—your people, messages, etc—unless you grant them access in Account Settings > Privacy & Data. To grant access, you must be an Account Admin or Member with the account-level permission, “Enable access for support teams.”
You might grant us access to help you troubleshoot issues, etc. Enabling the Support Team Access or Customer Success Team Access (for Premium customers) settings grants authorized Customer.io personnel access to your account. You can disable this setting to revoke access at any time.
| Access Setting | Max Time | Grants |
|---|---|---|
| Support Team Access | 180 days | Read-only access to members of the Technical Support team—and people operating in a Technical Support capacity—while providing support. |
| Customer Success Team Access | 180 days or indefinitely | Read and write access for your Primary CSM. Other CSMs have read-only access |
Reporting a security concern
If you see a hole in security or an area that we can improve, send us an email to win@customer.io. We’ll work with you to make sure we understand the issue and address it. We consider security correspondence and vulnerabilities our highest priorities and will work to address any issues that arise ASAP.